Cyber Crime News | MATA: A Multiplatform Malware Framework
In the latest Cyber Crime News, Kaspersky experts recently uncovered the malicious MATA framework. Hackers are targeting Windows, Linux, and macOS operating systems using this malicious MATA framework. Cybercriminals were using it to attack corporate infrastructures around the world. It can work under various operating systems, and it boasts a wide range of malicious tools.
The first artifacts we found relating to MATA were used around April 2018. After that, the actor behind this advanced malware framework used it aggressively to infiltrate corporate entities around the world. We identified several victims from our telemetry and figured out the purpose of this malware framework.
MATA Background:
It is said that this MATA malware framework has discovered and linked to the notorious North Korean hacking group known as Lazarus. Dubbed “MATA,” the framework has apparently been in use since around April 2018, mainly to aid in attacks designed to steal customer databases and distribute ransomware.
“Malicious toolsets used to target multiple platforms are a rare breed, as they require significant investment from the developer,” the report said.
Such tools are deployed in a way that attackers can leverage them over a long period of time.
In the series of cyber-attacks discovered by Kaspersky, the MATA framework was able to target three platforms – Windows, Linux, and macOS.
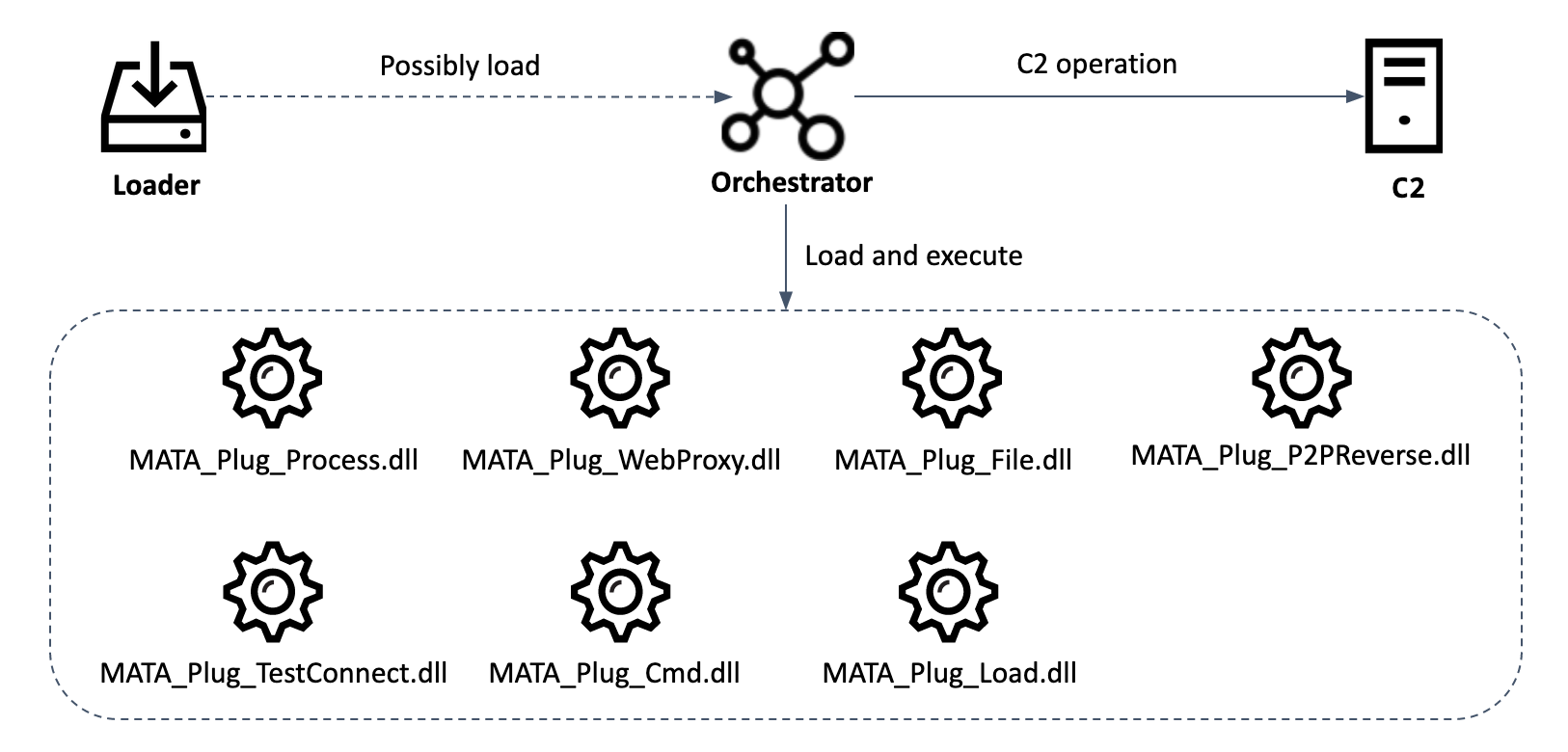
Depending on the characteristics of the specific attack scenario, the modules could be loaded from a remote HTTP or HTTPS server, from an encrypted file on the hard drive, or transferred through the MataNet infrastructure over a TLS 1.2 connection. The assorted MATA plug-ins can:
- Run cmd.exe /c or powershell.exe with additional parameters and collect responses to these commands;
- Manipulate processes(remove, create, etc.);
- Check for a TCP connection with a specific address (or range of addresses);
- Create an HTTP proxy server waiting for incoming TCP connections;
- Manipulate files (write data, send, delete content, etc.);
- Inject DLL files into running processes;
- Connect to remote servers.
If You Want To Get More Daily Such Jobs Updates, Career Advice Then Join the Telegram Group From Given Link And Never Miss Update.
Join Telegram Group of Daily Jobs Updates for 2010-2021 Batch: Click Here
Why You’re Not Getting Response From Recruiter?: Click here
How To Get a Job Easily: Professional Advice For Job Seekers: Click here
Cognizant Latest News: Up To 20K+ Employees Will Be Hired: Click here
COVID-19 Live Tracker India & Coronavirus Live Update: Click here
Why Remove China Apps took down from Play store?: Click here
Feel Like Demotivated? Check Out our Motivation For You: Click here
List of Best Sites To Watch Free Movies Online in 2020: Click here
5 Proven Tips For How To Look Beautiful and Attractive: Click here